Class 10 Computer MCQ
Class 10 Computer MCQ: Preparing for your Computer Applications does not require a large amount of time, but rather a little amount of effort and understanding of computers and their applications. Computer Applications, in contrast to more difficult subjects that demand consistency, hard work, and some skill, is a simple subject. We’ve got your back at Adda247. We’re all aware of how difficult it is for you to study for the exams. To help you reach your objectives, we’ve put up a selection of MCQs that will help you prepare for the CBSE Class 10 Computer MCQ. The solutions to the CBSE Class 10 Computer Science MCQs are also included in this post. Check out CBSE Class 10 Computer Applications Important MCQ Questions With Answers before you leave, and good luck on your CBSE Class 10 Computer Applications MCQ for exam!
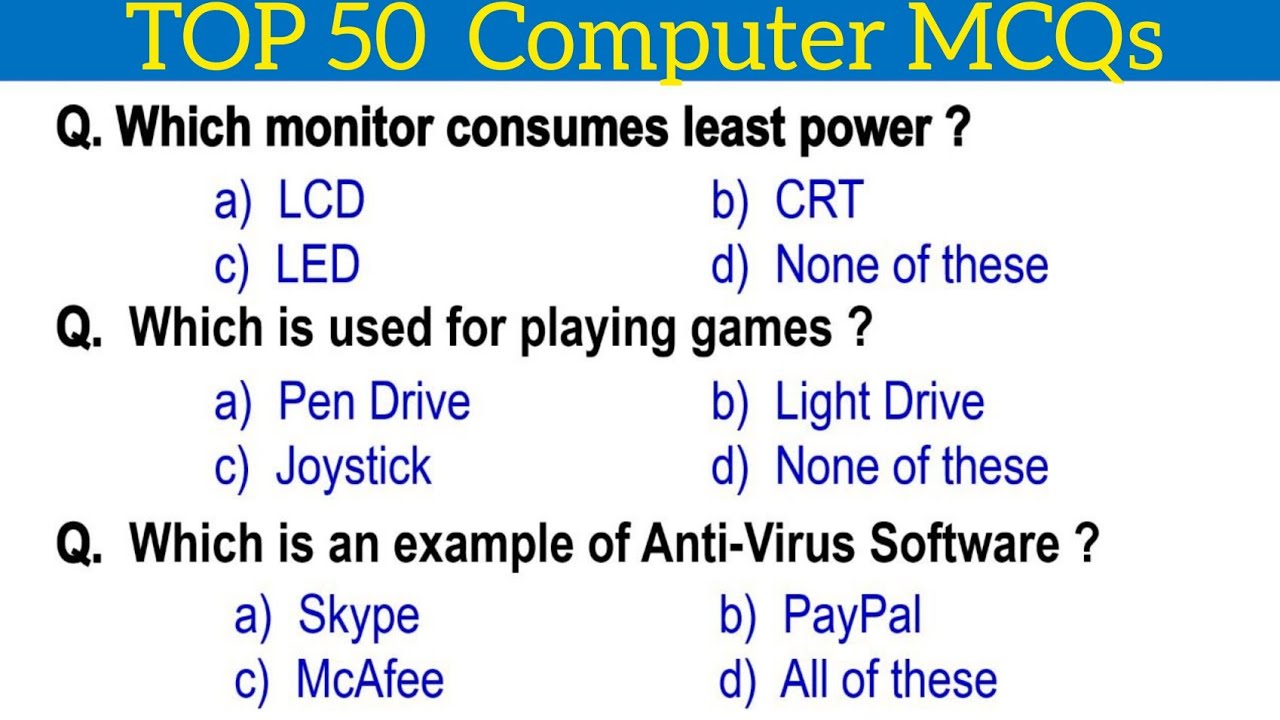
CBSE Class 10 Computer MCQ
Q. General purpose computer are used for:
(A) Creating a small database
(B) Performs calculation
(C) Accounting
(D) All of the above
Answer: (D) All of the above
Q. The basic goal of the computer process is to convert data into:
(A) Graphs
(B) Files
(C) Tables
(D) Information
Answer: (D) Information
Q. The following has highest Access time:
(A) Magnetic disk
(B) Swapping devices
(C) Floppy disk
(D) Cache
Answer: (A) Magnetic disk
Q. Error detection at data link level is achieved by the following
(A) Equalization
(B) Bit stuffing
(C) Hamming code
(D) Cyclic redundancy codes
Answer: (D) Cyclic redundancy codes
Q. A hardware device that is capable of executing a sequence of instructions is called
(a) CU
(b) Processor
(c) CPU
(d) ALU
Answer: (b) Processor
Q. Computers that are portable and convenient for users who travel are known as
(A) Laptops
(B) File servers
(C) Supercomputers
(D) Minicomputers
Answer: (A) Laptops
Q. To transfer electronic mail from one machine to another, the following TCP/IP protocol is used
(A) RPC
(B) FTP
(C) SNMP
(D) SMTP
Answer: (D) SMTP
Q. High-resolution, bit-mapped displays are useful for displaying:
(A) more characters
(B) clearer characters
(C) graphics
(D) all of the above
Answer: (A) more characters
Q. The average number of comparisons in sequential search is:
(A) n2
(B) (n+1)/2
(C) n(n+2)/2
(D) n+2/2
Answer: (B) (n+1)/2
Q. The last DML statement processed during a commit transaction is?
(A) INSERT
(B) UPDATE
(C) DELETE
(D) POST
Answer: (A) INSERT
Q. Which of the following are computers that can be carried around easily?
(A) Laptops
(B) PCs
(C) Supercomputers
(D) Minicomputers
Answer: (A) Laptops
Q. The lowest level of input output control consist of
(A) Device drivers
(B) Interrupt handler
(C) both (a) and (b)
(D) None of these
Answer: (C) both (a) and (b)
Q. The following are the standard synchronous communication protocol except?
(A) SLIP
(B) SDLC
(C) PAS
(D) SMTP
Answer: (C) PAS
Q. The output of a lexical analyzer is:
(A) A parse tree
(B) Intermediate code
(C) Machine code
(D) A stream of tokens
Answer: (D) A stream of tokens
Q. Following is the Special software to create a job queue:
(A) Interpreter
(B) Linkage editor
(C) Spooler
(D) Drive
Answer: (C) Spooler
Q. First supercomputer developed in India is
(A) SHIVA
(B) PARAM
(C) ARYA BHATT
(D) BUDDHA
Answer: (B) PARAM
Q. The time required for a gate or inverter to change its state is called
(A) Propagation time
(B) Decay time
(C) Charging time
(D) Rise time
Answer: (A) Propagation time
Q. Standard for MODEM is drawn up by the following organisation:
(A) Hayes
(B) AT and T
(C) BELL
(D) CCITT
Answer: (D) CCITT
Q. The following topology has highest reliability:
(A) Ring
(B) Mesh
(C) Bus
(D) Star
Answer: (B) Mesh
Q. Which of the following is NOT associated with Computers?
(A) Screen
(B) Mouse
(C) Bit
(D) Pencil
Answer: (D) Pencil
Q. Supercomputer developed by Indian scientists
(A) Blue Gene
(B) Param
(C) Super301
(D) Compaq Presario
Answer: (B) Param
Q. Dirty bit is used to show the
(A) Page with corrupted data
(B) The wrong page in the memory
(C) Page that is modified after being loaded into cache memory
(D) Page that is less frequently accessed.
Answer: (C) Page that is modified after being loaded into cache memory
Q. The following is the unstable sorting method?
(A) Insertion sort
(B) Bubble sort
(C) Merge sort
(D) Heap sort
Answer: (D) Heap sort
Q. Personal computers can be connected together to form a:
(A) Enterprise
(B) Network
(C) Supercomputer
(D) Server
Answer: (B) Network
Q. The garbage collector
(A) is critical for efficient virtual memory system
(B) Prevents fragmentation from occurring
(C) Is mostly used with fixed partition
(D) Collects fragmented areas of memory
Answer: (D) Collects fragmented areas of memory
Q. The correct HTML code to display(P+Q)2 is:
a.<SUB>(P+) 2</SUB>
b.P+Q<SUP> 2</SUP>
c.(P+Q)<SUP> 2</SUP>
d.<SUP>(P+Q) 2</SUP>
Q. Which HTML tags cause browsers to render text as italics?
a.<text style = “italics”></text>
b.<ital.></ital.>
c.<i></i>
d.<b></b>
Q. The correct HTML code for inserting an image is:
a.<img herf=”image.gif”>
b.<img>image.gif</gif>
c.<image src = “image.gif”>
d.<img src = “image.gif”>
Q. Which attribute is NOT valid for the <body>tag?
a.background
b.color
c.vlink
d.bgcolor
Q. ____________attribute is used to specify the location of an image file.
a.alt
b.src
c.align
d.name
Q. Which of the following is NOT an example of Intellectual Property rights?
a.Patent
b.Trademark
c.Password
d.Industrial Design
Q. The_________ attribute of <img> tag specifies an alternate text for an image, if the image cannot be displayed due to any reason.
a.alt
b.alternate
c.tooltip
d.text
Q. While creating a Web document, which unit is used to express an image’s height and width?
a.Centimeters
b.Pixels
c.Dots per inch
d.Inches
Q. Preeti needs to send a very confidential message to her colleague in office over a secure channel. She uses a technique wherein an actual message (which is in readable form) can be converted into an unreadable message. This concept is known as________________
a.Encryption
b.Decryption
c.Plagiarism
d.Data Security
Q. The default alignment of images, that are inserted in Web page, is:
a.left
b.right
c.inline with text
d.middle
Q. Which of the following techniques can be used for security of data?
a.Authentication
b.Authorisation
c.Encryption
d.All of the Above
Q. Which of the following is not a cybercrime?
a.Plagiarism
b.Phishing
c.using licensed software
d.hacking
Q. _________ is a software for which exclusive rights of modification in the source code remain with the owner.
a.Free Open-Source Software
b.Freeware
c.Open-Source Software
d.Proprietary Software
Q. A _______________ is the right given by the government to an inventor to protect his/ her invention from being used/copied for a fixed period of time.
a.Copyright
b.Intellectual Property
c.Patent
d.Trademark
Q. Which of these is NOT an attribute of the font tag?
a.color
b.face
c.type
d.size
Q. The <_________><________> tag displays text in subscript form.
a.sub
b.sup
c.sups
d.subs.
Q. HTML tag to draw horizontal line:
a.<hl>
b.<hr>
c.<hline>
d.None of the above
Q. Secure data transmission means
a) Data is accessible by any unauthorized person during transmission.
b) Data can not be accessed by any unauthorized person during transmission.
c) Transmission of data happens easily
d) No one can access it
CBSE Class 10 Computer MCQ All Chapters
| 1 | Which one of the following software comes under Open-Source Software category?
a. Photoshop b. Ms-Paint c. Linux d. Windows |
| 2 | HTML tag to draw horizontal line:
a. <hl> b. <hr> c. <hline> d. None of the above |
| 3 | Secure data transmission means
a) Data is accessible by any unauthorized person during transmission. b) Data can not be accessed by any unauthorized person during transmission. c) Transmission of data happens easily d) Noone can access it |
| 4 | The correct HTML code to display(P+Q)2 is:
a. <SUB>(P+) 2</SUB> b. P+Q <SUP> 2 </SUP> c. ( P + Q)<SUP> 2 </SUP> d. <SUP> (P+Q) 2</SUP> |
| 5 | Which HTML tags cause browsers to render text as italics?
a. <text style = “italics”></text> b. <ital.></ital.> c. <i></i> d. <b></b> |
| 6 | The correct HTML code for inserting an image is :
a. <img href=”image.gif”> b. <img> image.gif</gif> c. <image src = “image.gif”> d. <img src = “image.gif” > |
| 7 | Which attribute is NOT valid for the <body> tag?
a. background b. color c. vlink d. bgcolor |
| 8 | attribute is used to specify the location of an image file.
a. alt b. src c. align d. name |
| 9 | Which of the following is NOT an example of Intellectual Property rights?
a. Patent b. Trademark c. Password d. Industrial Design |
| 10 | The attribute of <img> tag specifies an alternate text for an image, if the image cannot be displayed due to any reason.
a. alt b. alternate c. tooltip d. text |
| 11 | While creating a Web document, which unit is used to express an image’s height and width?
a. Centimeters b. Pixels c. Dots per inch d. Inches |
| 12 | Preeti needs to send a very confidential message to her colleague in office over a secure channel. She uses a technique wherein an actual message (which is in readable form) can be converted into an unreadable message. This concept is known as_
a. Encryption b. Decryption c. Plagiarism d. Data Security. |
| 13 | Which is the correct way to comment out something in HTML?
a. Using ## and # b. Using <!– and –> c. Using </– and -/-> d. Using <!– and -!> |
| 14 | The default alignment of images, that are inserted in Web page, is:
a. left b. right c. inline with text d. middle |
| 15 | Which of the following techniques can be used for security of data?
a. Authentication b. Authorisation c. Encryption d. All of the Above |
| 16 | Which of the following is not a cybercrime?
a. Plagiarism b. Phishing c. using licensed software d. hacking |
| 17 | is a software for which exclusive rights of modification in the source code remain with the owner.
a. Free Open-Source Software b. Freeware c. Open-Source Software d. Proprietary Software |
| 18. | A is the right given by the government to an inventor to protect his/ her invention from being used/copied for a fixed period of time.
a. Copyright b. Intellectual Property c. Patent d. Trademark |
| 19 | Which of these is NOT an attribute of the font tag?
a. color b. face c. type d. size |
| 20 | The < > tag displays text in subscript form.
a. sub b. sup c. sups d. subs. |
| Section-B
This section contains 20 questions. Answer any 16 questions. |
|
| 21 | Arun clicks on a link received in a message on his phone which promises him a complimentary trip to a destination of his choice. He forwarded this message to his friend, Panshul and asked him to do the same. But Panshul refuses and tells Arun that his personal and private information, such as online account names, login information and passwords can be stolen and he should be careful of such attacks.
a. Phishing b. Spamming c. Scamming d. Plagiarism |
| 22 | Consider the following HTML code:
<ol type=’i’> <li>First</li> <li>Second</li> <li>Third</li> <li>Fourth</li> </ol>
Choose the correct output that would be shown upon execution of the above code , from the choices given below:
a. I. First b. i. First II. Second ii. Second III. Third iii. Third IV. Fourth iv. Fourth
c. I First d. i First II Second ii Second III Third iii Third IV Fourth iv Fourth |
| 23 | Charlene is an artist. She displays her artwork on the Internet using her website to attract buyers. One day while browsing the Internet she discovers that another artist has displayed her painting portraying it as his own. Which right of Charlene was infringed?
a. Digital Privacy right b. Intellectual Property right c. Digital Property right c. Intellectual Privacy right |
| 24 | Which of the following will result in the largest text size? a. <H3> b. <H6>
c. <H2> d. <H4> |
| 25 | We can create a numbered list using the tag.
a. <UL> b. <list> c. <OL> d. <DL> |
| 26 | Which of these is NOT an example of Cyber bullying?
a. Copying a classmate’s personal photo against his/her permission from his social media account and sending it to other friends on their emails b. Bullying a classmate in the school corridor. c. Threatening someone on whatsapp. d. Posting mean messages about someone on their social media. |
| 27 | Identify which of the following type of list will create a bulleted list.
a. Unordered b. Ordered c. Definition d. Numbered |
| 28 | Which sequence of HTML tags is correct?
a. <html><head><title></title></head><body></body></html> b. <html><head><title><body></title></head></body></html> c. <html><head><title</head><body></body>></title></</html> d. <html><head><title><body></body ></title></head ></html> |
| 29 | Pratham is excited to use a new software which is freely available to download but he cannot modify or change the source code. Pratham is using
a. Freeware b. Open-Source Software c. Both a and b d. None of the above |
| 30 | Priyanshu has written the following code snippet as part pf an HTML program.
<B> Mystery Moon </B>
Predict the output of the above from the following: a. Mystery Moon b. Mystery Moon c. Mystery Moon d. Mystery Moon |
| 31 | Consider the following code:
<img src=”Computers.jpg” width=” ” height=” ”> Fill in the blanks to set the image size to be 250pixels wide and 400 pixels tall. a. 250, 400 b.400, 250 c. <250><400> d. <400><250> |
| 32 | Tag (s) required to create Description lists in HTML:
a. <DL> b. <DT> c. <DD> d. All of the above |
| 33 | Which of the following is NOT a reason for the digital divide in different demographic regions?
a. Cost of Technology b. Lack of information c. Lack of access to high performance computers d. Lack of access to the disabled. |
| 34 | One of the most popular method of encrypting data is Ceaser cipher where original data is replaced by a key character like if key is -2 than ‘a’ will be replaced by ‘y’, ‘b’ is replaced by ‘z’ and so on.
If the key is 2 i.e. Every letter is replaced by its next to next letter means the letter ‘A’ will be replaced by ‘C’, the letter ‘B’ is replaced by ‘D’, and so on then what will be the replacement of the word ‘CoMpUtEr’. a. Eqorwvgt b. eQOrwVtG c. eqroWVTG d. EqOrWvGt |
| 35 | Consider the following form control in a HTML form:
Male Female Now choose the correct line of code for the above : a. <input type = “radio” name= “Gender” value= “male”>Male<br> <input type = “radio” name= “Gender” value= “female”>Female<br> b. <input type = “radiobutton” name= “Gender” value= “male”>Male<br> <input type = “radiobutton” name= “Gender” value= “female”>Female<br> c. <input type = “radio”, name= “Gender”>< value= “male”>Male <input type = “radio”, name= “Gender”>< value= “female”>Female d. <input type = “radio” name= “Gender” value= “male”><br> <input type = “radio” name= “Gender” value= “female”><br> |
| 36 | Gagandeep has written the following code to display an image in the background of HTML document:
<BODY BgGround= “Animals.jpeg”> but he is not getting the desired output. Help him in identifying correct code from the following a. <BODY Bg= “Animals.jpeg”> b. <BODY BACK= “Animals.jpeg”> c. <BODY BGIMAGE= “Animals.jpeg”> d. <BODY BACKGROUND= “Animals.jpeg”> |
| 37 | Which of the following is a way to avoid Plagiarism when using material from the Internet?
i. Citing ii. Paraphrasing iii. Referencing iv. embedding
Choose the correct option: a. i and ii only b. Only i c. i, ii and iii only d. ii and iv only |
| 38 | Tag to create password field in HTML document:
a. <password> b. <input> c. <pwd> d. <pword> |
| 39 | Which of the following tag is used to define options in a drop-down selection list?
a. <select> b. <list> c. <dropdown> d. <option> |
| 40 | Which of the following is the correct way to create a list using the lowercase letters?
a. <ol alpha = “a” > b. <ol type = “a”> c. <ol letter = “a”> d. None of the above |
|
Section-C Case study based questions Section C consists of 10 questions. Any 8 questions are to be attempted. |
|
| Case Study –I
Geetika has recently created her social accounts. She is very excited as she waited so long to go online. She has recently also got admission in a prestigious high school and does not know many students. When she logs into her social media a few days later, she finds that someone is posting negative, demeaning comments on her social media profile. She is also getting repeated mails from unknown people. Whenever she goes online, she is trolled by multiple unknown people.
Based on the given information, answer the questions NO. 41-45. |
|
| 41 | Geetika is a victim of :
a. Eavesdropping b. Plagiarism c. Phishing d. Cyber stalking |
| 42 | Which of the following is the most appropriate action she should take?
a. She should stop going online and delete her social media accounts. b. She should NOT share this with anyone as she might face more of such kind of behaviour. c. She should file a complaint at the nearest police station. d. She should inform her parents and bring to the notice of school authorities. |
| 43 | After hearing her ordeal, the school decides to publish a set of moral principles that determines the appropriate behavior of students while using the internet. The school is referring
to a. Intellectual Property rights b. Internet Privacy c. Computer Ethics d. Cyber Ethics |
| 44 | Geetika is advised by her best friend, Seerat to protect her personal information from intentional or unintentional attacks by others. This is also known as
a. Digital right b. Copyright c. Data Privacy d. Intellectual property |
| 45 | The computer teacher of Geetika’s class decides to take an online session on the topic Netiquettes, which generally includes:
a. safeguarding one’s passwords and sensitive online information b. logging out of social media accounts after the session c. not bullying or trolling anyone by disrespecting them or passing inappropriate remarks d. All of the above. |
|
Consider the following code created by Sumantha for a webpage: <html> <body bgcolor=”yellow”> <center> <h1> Our Country : India < >———————————— line1 <imgsrc=”india.jpg”> </center> <p> <font color=”red” size=”5″ =”Times New Roman”>——— line2 India is spread over a large geographical area. In terms of area, it is the 7<sup>th</sup> largest country while in terms of population, it is the 2<sup>nd</sup> largest country in the world. Some facts about India are as follows< ></p>————— line3 <ul> <li>Area :Approx 3.28 million sq. km <_>————————- line4 <li>North to South extension :Approx 3,200 km</li> <li>East to West extension :Approx 2900 km</li> < >——————————————————————– line5 </body> </html>
Based on the given information, answer the questions NO. 46-50. |
|
| 46 | Choose the correct option from the following to fill up in line 1:
a. \h1 b. \h6 c. /h6 d. /h1 |
| 47 | Choose the correct option from the following to fill up in line 2:
a. font b. face c. type d. text |
| 48 | Choose the correct option from the following to fill up in line 3:
a. </f> b. <f> c. </font> d. <font> |
| 49 | Choose the correct option from the following to fill up in line 4:
a. <i> b. </li> c. <\li> d. <\i> |
| 50 | Choose the correct option from the following to fill up in line 5:
a. ul b. <\ul> c. <ul> d. </ul> |







 Karnataka 2nd PUC Result 2026 Date, Down...
Karnataka 2nd PUC Result 2026 Date, Down...
 RSKMP Result 8th Class 2026 Declared @rs...
RSKMP Result 8th Class 2026 Declared @rs...
 Karnataka SSLC 10th Answer Key 2026 Rele...
Karnataka SSLC 10th Answer Key 2026 Rele...